Welcome to the World of Standards!
ETSI enables chain of trust for digital signatures
Sophia Antipolis, 1 October 2015
First European Standard supporting European eIDAS regulation
ETSI has published the first of a series of European Standards to support the European Regulation on electronic identification and trust services for electronic transactions in the internal market, or eIDAS (Regulation (EU) 910/2014).
ETSI New Specifications on Scenarios for Emergency Communications in Disasters
Sophia Antipolis, 2 June 2015
Disaster situations often require additional emergency communications networks to be set up locally to enable responders (e.g. medical, rescue, care etc.) to coordinate their operations more effectively in the disaster area. To set up these networks efficiently, a standardized basis for estimating the capacity and other characteristics for communications by responders is highly desirable. This basis could then be used by many organizations including satellite network operators, equipment manufacturers and responders for design and development of systems, equipment and applications, not only for voice and data but also multimedia services.
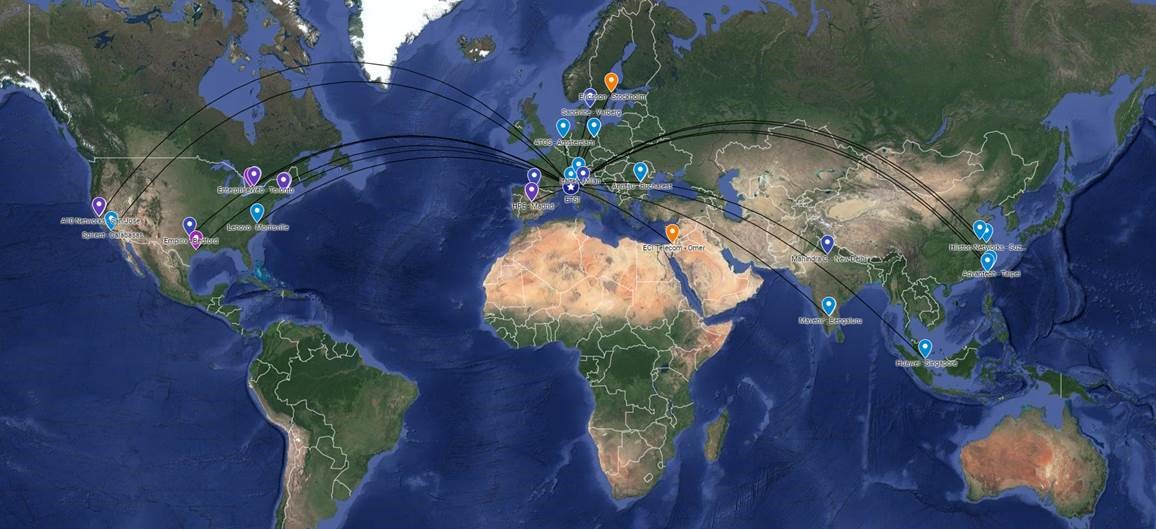
NFV Plugtests Programme
To accelerate NFV adoption and interoperability, a key enabler to NFV deployment, ETSI is running an innovative NFV Plugtests Programme.
The NFV Plugtests Programme provides a continuous and ubiquitous environment for collaborative testing and validation activities among different organizations.
The programme, leverages the ETSI Hub for Interoperability and Validation (HIVE) to interconnect participants’ labs and allow for multi-party interoperability testing, PoCs, demos, API validation, etc. Remote activities are complemented by periodic Plugtests events allowing the Programme community to meet and run face to face intensive testing sessions.
ETSI NFV HIVE is currently interconnecting over 40 remote labs and being key for the success of the preparation of the NFV Plugtests events as well as the OSM Hackfest activities.
The NFV Plugtests Programme is supported by a number of key open source communities working in NFV solutions, such as ETSI OSM, Fog05, kubernetes, ONAP, Open Air Interface, OpenDayLight, openslice, Open Stack and StarlingX.
The Programme is open to ETSI members and non-members free of charge. Organizations are invited to join by registering to an NFV Plugtests event or by contacting Plugtests@etsi.org.
Security algorithms
Introduction
An encryption algorithm is a mathematical procedure used to encrypt data. Through the use of an algorithm and a key, information is encoded into cipher text and requires the use of a 'key' to transform the data back into its original form.
Algorithms are an essential part of a technology to ensure effective and secure authentication, as well as to provide integrity and encryption. ETSI creates cryptographic algorithms and protocols specific to fraud prevention, unauthorized access to public and private telecommunications networks and user data privacy.
ETSI is custodian of these algorithms, as well as algorithms produced by other organizations. We are also custodians of other codes and test suites.
Our Role & Activities
ETSI Security Algorithms Group of Experts (SAGE) provides standards makers with cryptographic algorithms and protocols specific to fraud prevention, unauthorized access to public and private telecommunications networks and user data privacy.
The group's output includes algorithms for audiovisual services, 3GPPTM, DECTTM, GSMTM, TETRA, GPRS and Universal Personal Telecommunications (UPT). Where appropriate, the group collaborates with other ETSI committees and with other organizations in order to ensure that the algorithms produced fully meet the needs of the technologies and services in which they are used.
Mobile communications
In recent years most of the group’s work has been for mobile telephone standards – the Global System for Mobile Communication (GSM™), the General Packet Radio Service (GPRS), the Universal Mobile Telecommunications System (UMTS™), Long Term Evolution (LTE™), and most recently 5G – all radio technologies specified by the Third Generation Partnership Project (3GPP™). Indeed, all the standardized algorithms in UMTS, LTE and 5G mobile telecommunications, as well as more recent GPRS algorithms, have been specified by SAGE.
Whilst the algorithms are considered to be extremely robust, there is always a need to have alternative solutions ready should a breach of security ever occur. For this reason, the SAGE group develops new 256-bit algorithms – including radio interface encryption and integrity algorithms (for both user plane and control plane traffic) as well as authentication and key agreement (AKA) algorithms – to provide long-term resistance to possible future quantum computing attacks in 5G systems. These same 256-bit algorithms could also be potentially retrofitted to previous-generation mobile systems if required.
For more information see our section on Algorithms & Codes.